Three weeks ago, we published a blog post about the
Retefe banking Trojan
, which began targeting banking customers in the United Kingdom. The Trojan steals login credentials and other personal information. Retefe is usually spread via a phishing email. The email contains a document, which is embedded with malicious JavaScript and user interaction is needed to activate the Trojan.
Another UK bank has now been added to the list of affected banks. The main behavior of the Trojan has largely remained unchanged, with the exception of its malicious components. The infection vector, as well as the installation of the malicious certificate, are the same as we reported in our last blog post.
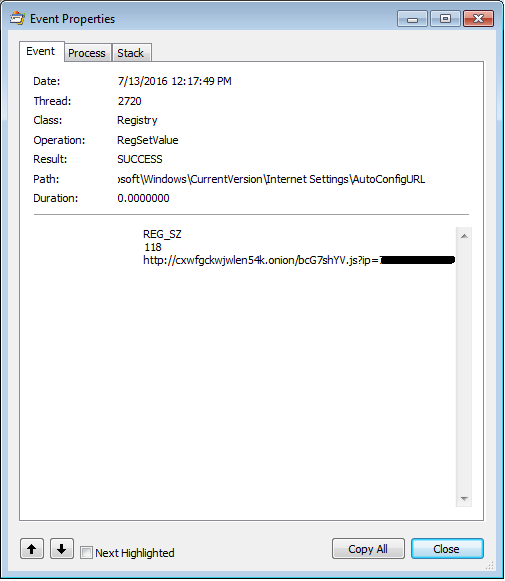
Once the JavaScript runs it attempts to kill open Web browser processes. It then installs a fake certificate and changes the proxy auto-config URL. All scripts are obfuscated with the Dean Edwards packer. This behavior is similar to the previous version of Retefe.
The JavaScript, however, now contains three powershell scripts, two of which are the same as in the previous version. ConfirmCert clicks “OK” in the window displayed during the installation of the rogue certificate and AddCertFF adds the rogue certificate to FireFox. InstallTP is the new powershell script. It downloads and installs three programs: Task Scheduler wrapper, Tor and Proxifier.
The Task Scheduler Managed Wrapper is downloaded from Codeplex. This adds the option to use the object “New-Object Microsoft.Win32.TaskScheduler.TaskService”, which is later used for establishing persistence.
The Tor client gives the Trojan the possibility to access .onion domains directly.
Proxifier, as stated on their website, “allows network applications that do not support working through proxy servers to operate through a SOCKS or HTTPS proxy and chains.”.
The AutoConfigURL contains a link to a .onion domain and it can be reached now because Tor was, installed.
![]()